Stored Cross Site Scripting (XSS) in Zoneminder – Up to 1.36.12
| Title | Stored Cross Site Scripting (XSS) in Zoneminder – Up to 1.36.12 |
| Discovery date | 16/05/2022 |
| Release date | 16/11/2022 |
| Credits | Mario Tommasino |
| Affected products | Zoneminder – Up to 1.36.12 |
| Class | Stored Cross Site Scripting (XSS) |
Disclosure timeline
| 16/05/2022 | Request for CVE ID |
| 16/11/2022 | CVE released |
Vulnerability Description
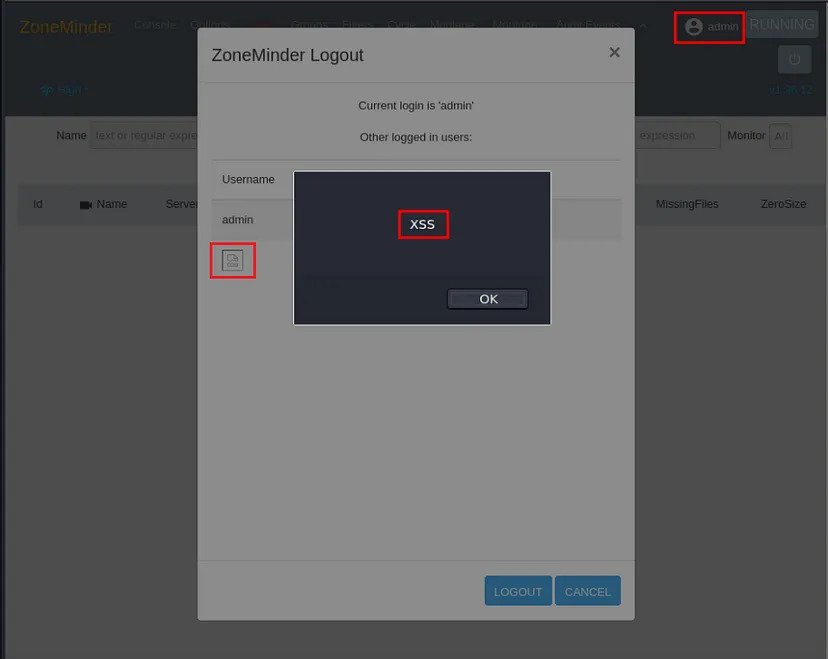
Stored Cross Site Scripting (XSS) exists in ZoneMinder up to v1.36.12. This allows an attacker to execute malicious code via the “Username” vulnerable field when an Admin (or a user that can see other users logged on the platform) clicks to logout.
Affected Assets
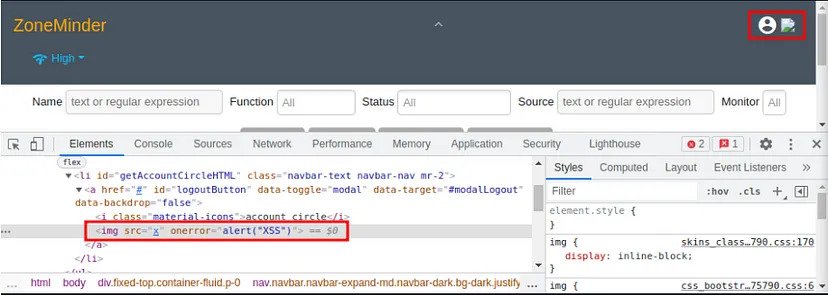
Username field and logout function.
Payload
<img src=x onerror=alert(“XSS”)>
Details
When a new user is created (or a user’s username is modified), if the “Username” field is set to an XSS payload (see Payload), at the next login with the modified username, if an Admin (or whoever has the proper permissions to see other users logged on the platform) want to logout from the web page, the “list of current user logged” triggers the payload and an you have an XSS. This works as long as the user with payload remains logged in.
Proof of Concept
1. Create a new user or rename an exixsting one and insert the payload as his username (see Payload)
2. Wait for the admin (or whoever has the ability to see logged in users) to log in and as long as you are logged in, if that user clicks to logout, the XSS is triggered because the logout function shows the users still logged on the platform and the code inside the username field is executed.